All multi-factor authentication (MFA) mechanisms can be compromised, and in some cases, it's as simple as sending a traditional phishing email. The latest phishing attacks can bypass Two Factor Authentication (2FA) protection without being noticed.
All multi-factor authentication (MFA) mechanisms can be compromised, and in some cases, it’s as simple as sending a traditional phishing email. The latest phishing attacks can bypass Two Factor Authentication (2FA) protection without being noticed.
Google researchers are seeing more phishing attacks that are 2FA-aware. Attackers know that organizations are embracing two-factor authentication as a means of thwarting phishing attacks seeking to compromise credentials.
Who Uses 2FA?
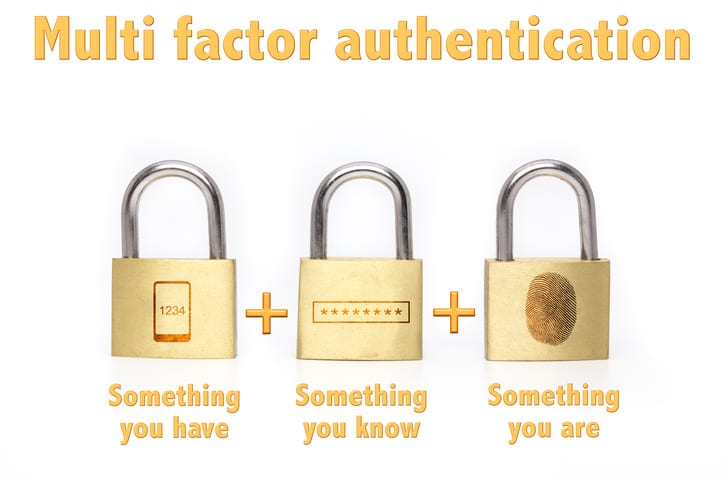
Decades of successful attacks against single-factor authentication methods, like login names and passwords, are driving a growing widescale movement to more secure, multi-factor authentication (MFA) solutions. Although MFA solutions have been available for decades, due to a variety of reasons, there is now an ongoing, wide scale, rapid adoption of MFA/2FA in both corporate environments and by internet websites.
This trend is exemplified by the fact that over the last few years, the most popular websites and services, including those owned by Google, Microsoft, Facebook, and Twitter, have offered 2FA solutions to their customers. Many internet sites and services now offer both traditional login name/password solutions and more secure 2FA options.
How Does 2FA Work?
Two Factor Authentication helps you protect your identity and accounts. More organizations are using it for its security and ease-of-use. You’ve probably already used 2FA. For example, when you go to the ATM to deposit or withdraw money, you swipe your bank card and enter your personal ID number (PIN).
It’s much the same when you go online to your bank account. You sign in with your ID and enter a passcode, but there’s one more step. A one-time code is sent to you via text message on your mobile phone or in an email. Once you enter this code on the bank’s website, you can get into your account.
How Are Hackers Bypassing 2FA?
By using a second authentication factor (which usually is an SMS text message-based verification code), attackers who only capture usernames and passwords have little use for the details collected.
Attackers exploiting authentication often look for weaknesses in implementations along the entire process. They will look to see if there are gaps in the linkages between the identity, authentication, and authorization…and there often is.
According to a recent talk with Gmail security engineering lead, Nicolas Lidzborski, cybercriminals are evolving the art of the credential phish, and are adding in mechanisms to capture and instantly use the combination of username, password, and verification code.
In essence, the bad guys have come to realize SMS-based verification will be a part of the process and have painstakingly built detailed lookalike login pages that not only accept user credentials but also facilitate making the Google request to provide the second authentication factor.
As the victim provides the details, the malicious webpage simultaneously logs on to gain access to their entire G Suite. Today, it’s Google — Tomorrow, you can expect attackers to attempt this on every 2FA platform that uses some kind of single sign-on.
How Can We Defend Our Business In Atlanta From This 2FA Phishing Scam?
This is a tough attack method to crack. The pages look identical. The process looks identical. So, the only thing that would stand out is the potentially abnormal email request to view something in the user’s Google account.
2FA is good, but don’t over rely your security assurance on it. It’s a good tool to increase security, but there is a huge difference between 2FA improving security assurance and it being unhackable. Understanding the difference is crucial to all entities and security administrators relying on MFA solutions.
Education Is Essential To Defend Your Business Against 2FA Scams
Your users should be educated to be mindful of emails that take them to any kind of logon page on the Web. Just because they are prompted to authenticate, doesn’t mean they just blindly should.
Ongoing Security Awareness Training can help your employees stay current with attack trends, methods, and techniques used, empowering them to know when they see something that just isn’t right, and how to avoid falling for even the most realistic scams that capture 2FA.
Key takeaways:
If you use or consider going to 2FA, security awareness training has still got to be a big part of your overall security defense.
Want To Know More About How To Defend Your Business In Atlanta Against 2FA Hacks?
This whitepaper below covers over a dozen different ways to hack various types of Multi-Factor Authentication and how to defend against those attacks. You will learn more about:
Download Your 12+ Ways To Hack Two-Factor Authentication White Paper
In the meantime, don’t take chances with the security of your data. To stay up to date on these and other IT topics, visit our Blog.
Call our business managed IT services department directly at (404) 777-0147 or simply fill out this form and we will get in touch with you to set up a getting-to-know-you introductory phone call.
Fill in our quick form
We'll schedule an introductory phone call
We'll take the time to listen and plan the next steps
11285 Elkins Rd Suite E1, Roswell, GA 30076
© Copyright 2025 Centerpoint IT. All Rights Reserved. Website in partnership with Tech Pro Marketing. | Privacy Policy
Get Immediate Help For All Your Technology Issues (404) 777-0147

If you want our team at Centerpoint IT to help you with all or any part of your business IT, cybersecurity, or telephone services, just book a call.
Fill in your information below to get started today.
"*" indicates required fields
Fill in your information below to schedule now.
"*" indicates required fields
Before your organization commits to 1, 2, 3 or even longer managed IT services contract, understand what you’re getting. Centerpoint IT gives you the facts in our Managed IT Services Buyer’s Guide.
Enter your information below and we’ll send it over.
"*" indicates required fields

We are turning 15 and want to celebrate this milestone with you because without you this would not have been possible. Throughout this year look for special promotions on services and tools aimed at Making IT Simple for You so you can focus on your business.

We are turning 15 and want to celebrate this milestone with you because without you this would not have been possible. Throughout this year look for special promotions on services and tools aimed at Making IT Simple for You so you can focus on your business.
https://calendly.com/centerpoint-it/discovery-call